Popular WordPress SEO Plug-in Vulnerability Affects 14 Million
Another week, another WordPress plug-in vulnerability. This time, the plug-in in question is the very popular WordPress SEO by Yoast plugin. According to Yoast’s site, the plug-in has been downloaded more than 14 Million times. In all fairness, it is the most well-known SEO plug-in for WordPress sites out there.
Just like the SlimStat recent plugin vulnerability, the bug in the WordPress SEO plugin makes your site vulnerable to SQL injection. SQL is the language that runs the back-end SQL database that powers WordPress sites. Through an SQL Injection attack, a malicious user could insert their won SQL code into your server through a known vulnerability. They accomplish this through a series of extra code at the end of a Web address on your site.
The WordPress SEO vulnerability only allows someone who is logged into your site to perform the code injection. However, the injected code could change or delete page content or expose usernames. Full technical details were explained earlier today by Graham Cluley.
What To Do:
Update WordPress SEO by Yoast to the latest version (1.7.4). Now.
Good practice also suggests to make sure former employees and other people no longer affiliated with your website (perhaps and old developer?) no longer have active accounts.
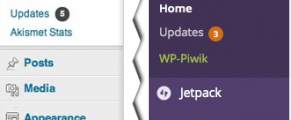 Log into WordPress and look for little icons with numbers next to the Updates menu item. If you see a number next to it, that number indicates the number of plug-ins, themes or other updates you need to execute.
Log into WordPress and look for little icons with numbers next to the Updates menu item. If you see a number next to it, that number indicates the number of plug-ins, themes or other updates you need to execute.
Simply click the update menu item, select all the updates on the page that follows, and click the Update Plugins button. It’s that simple and extremely important!


